After recently attending, participating, tuning in, engaging? in the event, I wanted to share some thoughts on the only conference out there that is solely focused on the detection engineering and threat hunting profession (as of Nov 2023, and from my potentially limited knowledge). Please correct me in I am wrong in that statement, I would love to learn of others.
Now I’m sure you’re aware of DEFCON, but have you heard of DEATHcon?
What is DEATH… Baby don’t hurt me
DEATHcon (Detection Engineering and Threat Hunting Conference), is promoted as an online and in-person hands-on conference for Detection Engineers and Threat Hunters.
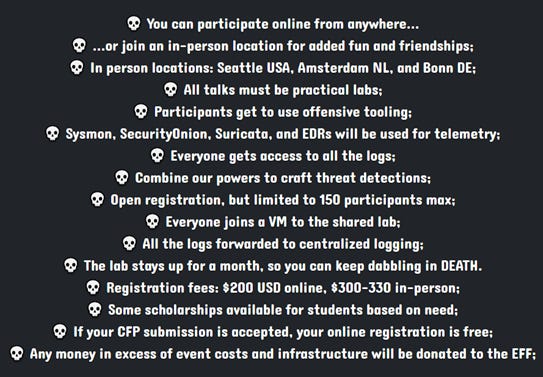
Here is some basic information about the conference.
The organizers of the conference are Tigran Terpandjian, Randy Pargman, and Olaf Hartong. Each very experienced and involved in the cyber research, hunt, detection, and intel communities. If you are really following this industry, you’ve heard of at least one of them. That knowledge would also probably be a good indication of your interest in this conference.
I would say that this event is most closely related to BSides meetups. The focus is on practitioners, and it is hosted/run by practitioners. There is a clear understanding of tools and processes, and presentations are given by analysts and tool developers themselves. Here is the link if you would like to find out more: https://deathcon.io/.
One thing that is important to know about DEATHcon, is that it is geared towards more advanced and senior practitioners. There are no restrictions against newbies or those with interest in the work, but there is definitely some prior knowledge required to really benefit from the labs and con (detection engineering and threat hunting are advanced roles as is, so naturally this makes sense). Here’s a short list of items you probably want to know a thing or two about before attending:
Virtual Machine set up and troubleshooting
VPN
Linux and Windows OS
Networking, you’ve probably set up a network or two in your time here on Earth
Application installation on Linux
SIEM usage
Query languages/scripting
Red teaming, ATT&CK, the adversary mindset
You’ve seen a log or two, maybe you can even read them
Now if you would like to learn more about detection engineering, threat hunting, and other aspects of threat-informed defense, you can check out my collection of resources, guides, and tools here: https://start.me/p/X25q7l/threat-informed-defense-ecosystem. I also made a short blog post about the project →
Be on the lookout for a fairly significant update in the coming months to this project. I’ve found a new section to add, and will probably break up some existing ones into beginner and advanced groups.
Now back to the regularly scheduled program.
While DEATHcon is a 2-day event, there are wayyy more workshops than one could view in that time span. However, unlike other conferences, you don’t need to pick and choose which ones you’ll attend. The presentations and labs stay up for nearly a month afterwards, allowing for every workshop to be viewed, if you so desire. Communication and interaction with everyone else attending, if you are virtual, is probably best during those two days. However, most workshop speakers did say that they are always open to good chats after the event. You are put in a Slack channel for the event, where all videos, lab info, and chats occur. I personally missed out on good interactions as I had a few conflicting time sinks during the official event.
The basic workflow was that you would enter a slack channel specific to the workshop, read up on any intro info and watch a video demo/presentation, then access the lab and go forth and concur. Each lab differed widely based on workshop, so any next steps would be unique. You may be accessing Splunk, Elastic, a linux machine, web GUI, etc. There really was a lot of different tools in use.
Prior to the start of the conference, small slack channels were created by geographic regions. This allowed you to interact with others in their same time zone. My group took home the most quiet group honors, take that extroverts #squadsoutheast. I don’t know what all was discussed in other groups, but it looked like most interactions occurred in the workshop specific channels.
One thing that is awesome about this approach is that you get to see how easy it can be to set up a detection engineering or threat hunting home lab. Lots of the labs can be made by individuals at home for further practice or usage. The knowledge gained when you setup something yourself cannot be overstated.
Workshops
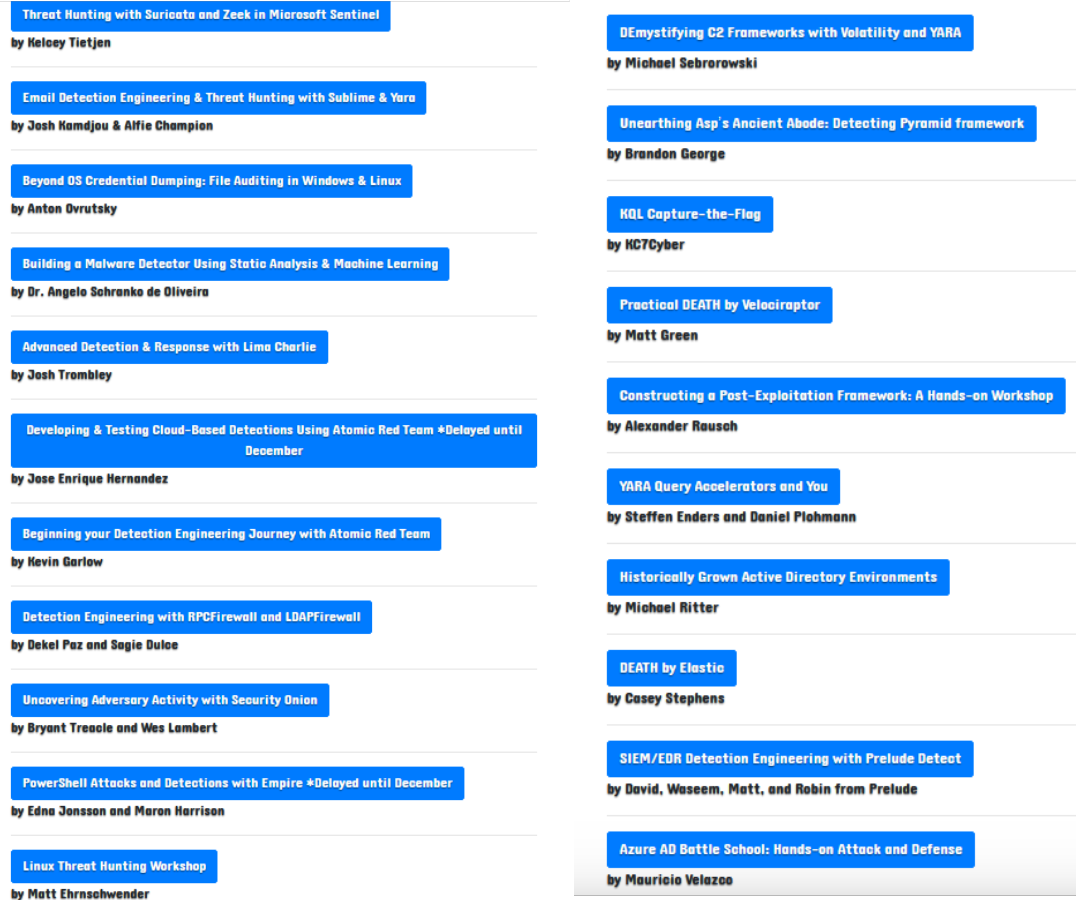
Now let’s get into the actual presentations of the con. Here was the full list of workshops at DEATHcon 2023.
As you can see, lots of topics are covered here. Elastic, YARA, Empire, Velociraptor, AD, Azure AD, linux hunting, PowerShell, Lima Charlie, Atomic Red Team, Suricate, Zeek, rsyslog, Sysmon, Microsoft Sentinel, Splunk, EDR, and much more. I think this is a good variety of topics and processes, and they really did hit on many of the skills used by threat hunters and detection engineers. I would have liked to see some discussion on detection lifecycle or detection as code organization, and maybe I just missed some of that. There was talk on tuning and modifying detections to reach appropriate alerting percentages and criteria.
With a limited number of tickets available, this is one conference that you need to stay on top of so that you can get in before they sell out.
As with any low budget, decently complex network, there was a few hiccups surrounding usage and systems. This is to be expected, and the creators have day jobs, so you can’t fault them.
As a bonus, in the slack there was a channel dedicated to random death metal songs and death memes. So if that’s your thing, even more reason to join next year.
Quick tip, definitely set up your VM(s) prior to the event starting. I didn’t do this until the night before, big mistake on my part.
Final Thoughts
I’ll leave you with a quick glance of my thoughts on DEATHcon.
Positives:
$200 isn’t that much of an ask
Good variety of tools, processes, and topics
Hands-on
Taught by practitioners with advanced knowledge
No fluff or product selling
Ability to get inspiration for your own home lab for DEATH activities, and you can utilize labs long after the event ends
This con really is only for those interested in DEATH. You won’t likely find stranglers here.
Negatives:
There’s a bit of time/resources needed for setup of vms and labs
Some prior knowledge is required
This was just the second year of the event, and I am sure DEATHcon will continue to grow and produce more detection engineering and threat hunting fun.