In my last blog post, I covered the problems that SMBs face when it comes to cybersecurity and protecting their own organization and America’s supply chain. The difficulties mentioned included a lack of skilled cyber personnel, a lack of funding, cyber programs that are only focused on compliance actions, and the lack of relevant, useful, and up-to-date products that are geared towards SMBs. Go to The SMB Cybersecurity Problem to read the entire conversation. Having the full picture will help you understand this problem and why the solutions I am presenting here could actually assist in solving some of the problems small and medium-sized (SMB) businesses face when it comes to cybersecurity.
Before we dive in, we should probably discuss why this situation even matters? Why do we really care if the small companies have bad security? They’re too small for adversaries to think about anyways, right? Well, small and medium-sized businesses (SMBs) make up essentially 99% of the businesses in the United States. While they only account for around 45% of GDP, their presence allows for every organization to function. It may seem like large companies already do everything, but without SMBs, we really do not have an economy. Not to mention the innovation that SMBs develop and provide. While SMBs possess just a fraction of the $ as large orgs, they are a great stepping stone for someone looking to compromise the bigger entities. Remember how the Target breach originally happened? A third-party HVAC vendor had their credentials stolen. Sometimes the best way in is through someone else who already has the keys. Cybersecurity matters for every business, there are no passes, especially if the company does direct work with the government or other critical sectors.
In this post, when I talk about SMBs, I’m mostly referring to government contractors, critical infrastructure suppliers, and manufacturers. Tom’s Hotdog Stand does not make this list (but trust me I do love a good food truck). The focus is on businesses that are pertinent to a country maintaining their infrastructure, defense, and resources.
The Options
Let’s run through the most realistic options that SMBs have to address their cybersecurity needs. These needs might be identified by a compliance framework (PCI-DSS, CMMC), they might be identified by the CEO (prevent ransomware), or they may have no idea that they need better security (we’re just fine guys, no way we could be a target). For the needs/solutions, I am basing it on the knowledge I have gained by working in this field. While the list of solutions will include the most likely manners towards increased security, the “best” option is going to be different for each company, there is no standard way of achieving security. It really is unique in every situation.
I see four main options for SMBs to improve their cybersecurity posture.
- Outsource it
- Go fully cloud
- Create a team
- AI (jk lol this is so far from the answer)
Truth be told, some mixture of all 3 is probably the most likely avenue that would work long-term. Unfortunately, you’ll also notice that there is no “cheap and easy” route. They all have unique costs. Even if open-source tools and products are used, a team is still needed to build and utilize them. Or if you decide to outsource some things, you’ll save on costs for products and workforce, but lose out on customized security actions and processes. There is no magic product to ensure security, it can’t be done in 6 weeks (consulting orgs lie), and you can’t buy it (ask the Fortune 100s). Cybersecurity is a fine tightrope that businesses must walk, so without further ado, let’s jump in.
Option 1 – Outsource as much as possible
I’m going to start with this option since it seems to be the “go-to” for most small companies/owners. I’ll be honest, this is not my favorite choice, but that opinion is much easier to hold as someone who works in cybersecurity and has high standards. Sometimes this method can make the most sense for a business. Let your company focus on what you do for business and let someone else focus on the security. Seems like a decent idea. Businesses have outsourced things like HR, finances, IT, and marketing for ages, so why not security too? The difficulty with outsourcing security is where to define the scope of tasks. This also differs by organization. Since cybersecurity means something different to each person, you cannot easily hire a company to perform “cybersecurity” for you. Often, SMBs only hear about the cyber requirements that they must meet for regulatory purposes (scary CMMC, boooo), and that is the extent of their requests for assistance when it comes to cyber defense. So the SMB may hire a consulting firm to help them meet CMMC requirements, but they’ll totally miss out on every other aspect of security that is not listed in CMMC, with is like almost all of it besides some organization skills, basic controls, and policies. I have yet to identify a managed service that will actually take on 100% of the security tasks for a business.
For me, the unique environments, situations, and personnel of each business are why I do not particularly like MSSPs, or the idea of fully outsourcing security. To be effective, the MSSP must create solutions that can be plug-and-play to fit into any environment. This can work, but I’ve seen and heard of so many bad MSP/MSSPs, that I’m not confident until I see it in action. Honestly, my big concern here is that the MSSP usually doesn’t truly know the whole environment. They only have visibility into what their agents are installed and working on. Also, since the MSSP can’t really assume responsibility for security, they don’t have to improve much. Why increase MTTD and patching metrics when the customer never even notices anyway? The outsourced team can assist in security practices, but they aren’t owning the security in a way that a security manager or internal team would. When everything is standardized, it’s one-size-fits-all and each company is treated the same. This doesn’t bode well with threat modeling. This is also a reason why government compliance frameworks fall short, they are made for the masses, and unique situations are never taken into consideration. With all that said, I REALLY do not like the idea of Ed from finance doing the security, so if you must, well you must.
Another item to consider when looking to outsource security work is what exactly are you paying for, and what are you looking to outsource? An MSP is different than an MSSP. An MSSP is different than a SOC or MDR, and all of it is different from a complete security program that consists of GRC, Security operations, and security engineering/infrastructure. If you pay for a SOC, don’t expect policies, security controls, and system management. If you hire a consultancy for compliance, you won’t get network monitoring or threat hunting. Unfortunately, a complete security program cannot be outsourced (unless I’m unaware of a company that will actually do everything, in which case I have some serious questions for them). Maybe if you have a vCISO and a small internal team you can get close to a complete solution? I have never worked with an organization that utilizes a vCISO, so I’m not sure of their typical scope.
If you are going to outsource security, please please please ask someone who knows or has used the service provider in question. Again, the amount of MSP/MSSP/MDRs that are worth a darn thing are few and far between, based on personal experience. If you want the best, look into Huntress, Optiv, or Black Hills Information Security. These companies actually do good work, from what I can tell online (I do not have first-hand experience with either).
Option 2 – Go cloud
If it makes sense from a business perspective, the cloud can be a very good option for SMBs. Cloud deployments allow for the business to not really need a whole team in place for IT. Maybe one or two admins, and an analyst or two would suffice. As well, systems will be modern, functional, and likely somewhat secure (to a very limited extent, cloud security is entirely based on how you protect your data with controls and settings). Unlike the large businesses that require huge amounts of compute and storage, have internal teams in place, and have budgets that can cover large costs, SMBs need a lot for a little. Cloud costs can actually work in the favor of SMBs here, with all things considered. The cloud allows for more to be done, with a smaller workforce, and no physical location or space restrictions.
The low cost is especially true when utilizing a security platform, such as Microsoft E3/E5. The value and services you get from these licenses equate to an on-prem deployment that would require somewhere between 5-15 servers, a dedicated IT team, and other security solutions such as email filtering, VPN, SIEM, EDR, configuration management, identify management, SSO, etc. If you only utilize Windows OS systems and have no need for on-prem servers or storage, this is an even better deal. Now I am not saying that Microsoft’s cloud suite is easy to use, or that there are no other problems that arise due to this setup. I tried using Intune for a couple of months and could never get it working as I wanted. Of course, you need someone who can properly utilize the cloud products and is able to learn on the fly (Microsoft will change product names twice before you finish reading this blog), but with the right small team, a lot can be accomplished.
If the MS platform isn’t used, then most likely the business will go with offerings from its NGFW hardware vendor, such as EDR/AV, DNS filtering, IDS, VPN, and more from Palo Alto, Fortinet, or a similar vendor (wow there are too many acronyms in this here profession ladies and gents). The big issue with the cloud is that while infrastructure may exist virtually, you still have to do the GRC aspect. Microsoft isn’t going to pass your audit for you. So, while you can take aspects of the infrastructure side from Microsoft, there are still a lot of processes, policies, and planning that will need to be accomplished. That also doesn’t include monitoring of user activity within the cloud. You will still need someone who can analyze activity, respond to threats, and identify malicious traffic. The cloud makes things easier to scale and build, but it does not make it easier to secure or protect. Really the cloud just changes the boundary from network to identity. Side tangent, don’t buy into all that zero-trust stuff either. Most of the time, it is just a buzzword, and people have different definitions for what it actually means. What you need to know is that in your cloud environment, you want least privilege, least access, and the ability to granularly control permissions, based on more than just RBAC. You also want solid plans for activity monitoring, backups, and software patching. Those cloud recommendations come free of charge from “I’ve seen too many intel reports and opinions” Inc!
Option 3 – Build a team
Another option is to go “old school” and utilize an internal team. By team, what I really mean is AT LEAST 3 people. One IT/Engineering admin, one security operations member, and a GRC analyst / security manager. If the SMB can afford to have 3 people dedicated to internal security, the business can be in a very good place. However, most SMBs have one IT person at most, and this person is already overworked. Security CAN’T be added onto the task load of a single IT admin. That is a surefire way to lose that employee for better pay and an easier role elsewhere. To cover GRC, security engineering, and SecOps, I recommended having three employees at a minimum on the security team. You may be able to get away with no dedicated security members if you are Tom’s hot dog stand, but if you’re a defense contractor you really need to prioritize 2-3 people to get a hold of compliance and security. Most SMBs do not, and that is why it takes 3 years to get NIST 800-171 just 50% implemented. In all honesty, 800-171/CMMC could be completed in 6 months for a very cheap price. It is very much process-based with “define as you like” requirements. This also means that adversaries laugh at CMMC, as it is not going to better protect your organization unless you really have a special person working security/IT. CMMC isn’t the answer, but since many SMBs still give out admin rights to all users and barely update anything, it’s definitely a starting point.
Once a team has been formed, depending on skill and infrastructure in place, there are many great cost-effective products that can be obtained. For example, just a glimpse of what could be utilized without licensing costs -> Wazuh for EDR, ELK stack for SIEM, Security Onion for nearly full SOC coverage, Snort or Suricata for IDS, and FreeIPA/Keycloak for User Directory/SSO, and Caldera for control testing. Most of these items will require costs for the hardware side, but that too can be done in relatively cost-effective manners.
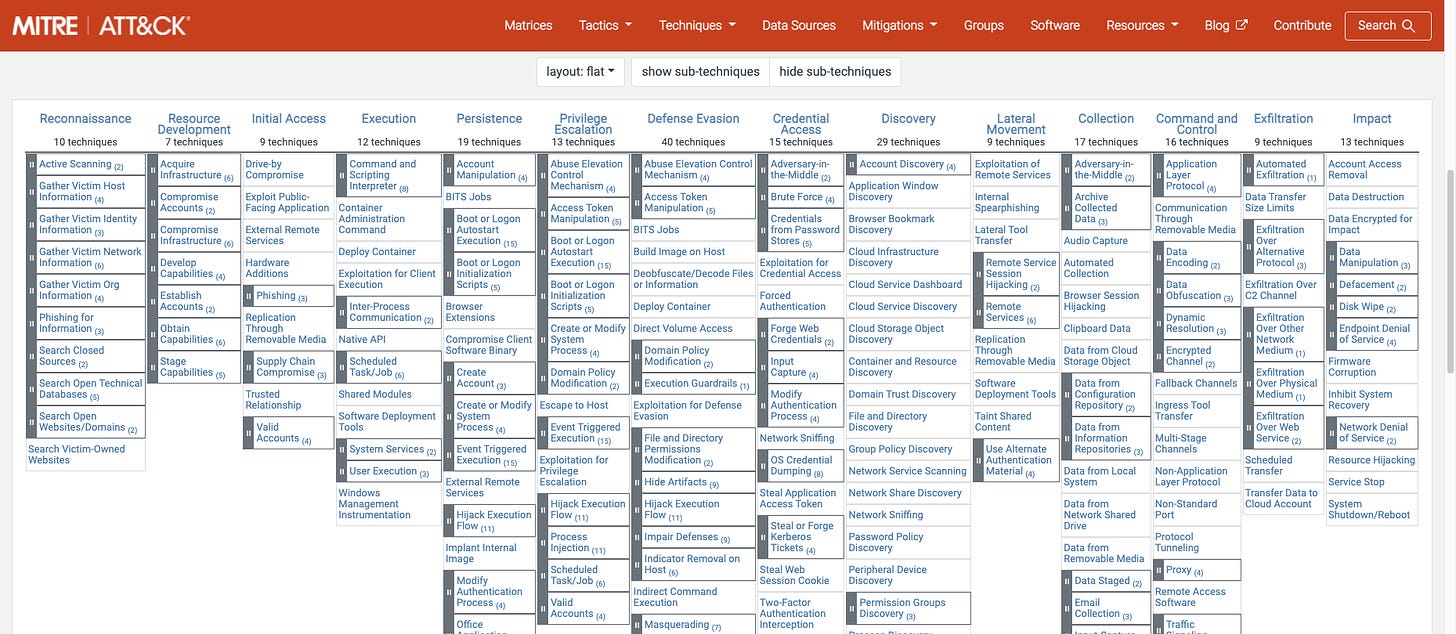
The most challenging part of building an internal team is going to be finding and retaining talent. There is a direct correlation between skill and effectiveness of a security team. And there is no easy way to identify who can be/is a skilled security practitioner. I’ve seen a lot of cert holders who have worked at larger organizations with limited talent, and people you’ve never heard of who are tremendous. Without the name, budget, opportunity for learning/advancement, and the allure of large organizations, SMBs lose out on a lot of cyber talent. Lack of expertise is the largest reason that SMBs do not generally have good cybersecurity. You could argue this is directly related to budget, location, and/or talent pipeline, and I can’t really disagree, but what cyber comes down to is practitioners who are able to protect against most common attack vectors. If an APT targets an SMB, they will likely get in (our most talented and valuable cyber companies can’t stop Volt Typhoon, so Joe’s Wild Wheelbarrows won’t stand a fighting chance). But whether that adversary lives in the environment for 8+ months is another story. Detection is a really important aspect of cybersecurity. You can’t just install some preventative controls and call it good. SMBs need to get a lot better at detection because no one can successfully prevent all attacks.
How I Would Secure an SMB
If you want my opinion, which if you are reading this, I suppose you do, this next part is how I would recommend an SMB to approach cybersecurity for their business. It is not perfect, but no option is. We cannot pretend to have the perfect answer or single best method to create a good cyber defense program. As I’ve said earlier, each situation is different, and no one is batting 1000% against adversaries. Intrusions do and will happen, preventing as much as possible and detecting/stopping the ones that do occur is really the goal of cyber defense. There is a reason defense in depth is still worth something. Initial access happens, but can we respond and stop the attack before it reaches impact?
Let’s just assume that our organization has 30 employees and is starting from nothing. No security team, barely any IT or looking/willing to overhaul everything. First step, hire an IT admin and a cybersecurity manager. You will be handling the GRC tasks internally. This means your cyber manager should be able to work with your IT admin to fully implement and develop compliance framework controls, guide risk decisions, and maintain accurate understanding and oversight of any sensitive information. The IT will need to be modern, so you can’t be using Windows 7 or CentOS devices anymore. Next, hire a consultant or cyber engineer for effective security design/implementation of preventative controls. This individual will assist with the security portion of the compliance framework, as well as build out further controls that prevent intrusions. This individual should be able to test defenses and spend some time with cyber threat intel (free stuff is fine) learning about TTPs adversaries are using. Last, hire a SOC/MDR service that does a good job of detecting and responding to incidents or active attacks. This mixture of a cybersecurity manager, consultant/engineer, and hired SOC/MDR service would get you as close as possible to a holistic security program. Depending on company growth you will need to hire more, but starting with an IT admin, manager, and engineer should safely get you across the compliance barrier and towards the path of active prevention.
As much as I love internal teams, I know the talent is hard to find, not always affordable, and risky with possible turnover in the field. But I am of the mind that someone in charge needs to be the organization. If you outsource the leadership portion, they will not always do what is in the best interest of your company and be less inclined to improve the defense program. You can outsource the SOC and maybe even design tasks, but the ship needs to be headed in the right direction for everything to work. Working to bolster cyber defenses will have a cost, but security is not something to roll the dice on, especially if your country is counting on you.