If you have been around cybersecurity long enough, you have probably heard the phrase “we just need to get ahead of the threat” at some point. Typically, this phrase is used by vendors looking to sell a product or idealists who don’t fully understand the complexities of cybersecurity. While the intentions behind that phrase may be good, it’s the wrong objective and is quite literally impossible. There is no “getting ahead” of the threat, but there is ability to reduce the risk a threat poses. One way to understand the relationship between threats and security is by comparing it to America’s pastime, baseball.
The word “security” means freedom from danger or threat. The dynamics of securing an enterprise’s operational functionality and its sensitive information requires a few assigned roles. First, an aggressor or threat that is to be protected against, and second, a person or team that is working to maintain the C-I-A (Confidentiality, Integrity, Availability) of the sensitive information and systems. Threats are typically someone or something that looks to steal information, inflict damage, or obtain financial gain. The defenders are people who spend their time working on safeguards, assessments, maintenance, and many other day-to-day actions. Unless speaking of a government agency, these teams do not engage a threat until it has been identified that they are actively attacking the organization. I’m going to use the game of baseball to explain why the goal of cyber defenders should not be to get ahead of the threat, but rather to create processes of scouting, preparing, and reacting that will give an organization the best shot at effective mitigation of its top cyber threats.
In baseball, the marquee matchup is the batter vs. pitcher.
The batter, who is known as the offensive positive in baseball, is more closely related to a cybersecurity defender. In baseball, the pitcher knows what pitch he is throwing, he has a good idea of what the velocity of the pitch will be, and if he is decent at his craft, he even knows the general location the ball will be at when it crosses the plate. As for the batter, all he can do is react to whatever pitch is delivered. The batter cannot “get ahead” of the pitcher. He can guess what pitch is coming, but if he is wrong, he will swing and miss faster than you can say “compromise.” While a .200 batting average is mediocre in baseball, it is very bad when it comes to cyber defense. Guessing is not an option in cybersecurity.
While the batter vs. pitcher is the main matchup, we must not forget that the batter is not only facing the pitcher but also the fielders. In the cybersecurity realm, we could consider fielders as those non-adversarial factors that restrict the ability to protect our stuff well. Things such as operational usage requirements, budgets, outdated compliance requirements, legacy systems, understaffing, pace of innovation, and even Bob from the Finance department. All these items play a part in the effectiveness of cyber defense programs. A truly accurate picture of cybersecurity is not a battle between cyber defenders and adversaries, but the security team vs everything that takes up their time, effort, and attention.
What can a hitter do to increase his odds of success in the box? It all starts even before the game begins. Top-tier hitters will scout the pitcher, learning information such as how fast he throws, his accuracy, his go-to pitches, and even if he can throw curveballs for strikes. This information helps the batter understand how the pitcher is likely to go after him. The batter must also know his strengths and weaknesses. If he cannot hit a curve ball, he may as well not swing at any and hope they all drop out of the strike zone as balls. For optimal odds at getting on base, the batter should know his opponent and himself very well.
While having that initial knowledge is great, the batter must also practice hitting. He cannot possibly be expected to execute if he relies on knowledge alone and does not develop skills. Batters need to practice hitting drills such as hitting off of a tee and underhand toss. Along with those drills, it is critical to get live reps at game speed. A batter will never be able to hit 90 mph if he practices at 65 mph. He must prepare for the real thing. Once it is game time, a hitter also needs to be paying attention to see the pitcher's rhythm and the game context. A 3-0 pitch with the bases loaded and no outs, is much different than a 3-0 pitch with two outs and nobody on base. As they say in baseball, the most important pitch is the next pitch. Things change fast and a batter needs to be ready to adapt to the situation.
Now even with all of that scouting and preparation, a hitter will still need to react to the specific pitch he receives to find success. He’ll have to time it right, make solid contact with the barrel of the bat, and then start running to first base. If his timing is off by milliseconds or his bat path has the wrong angle, he will swing and miss. The batter must utilize his knowledge, preparation, and reactions together for the best odds at success.
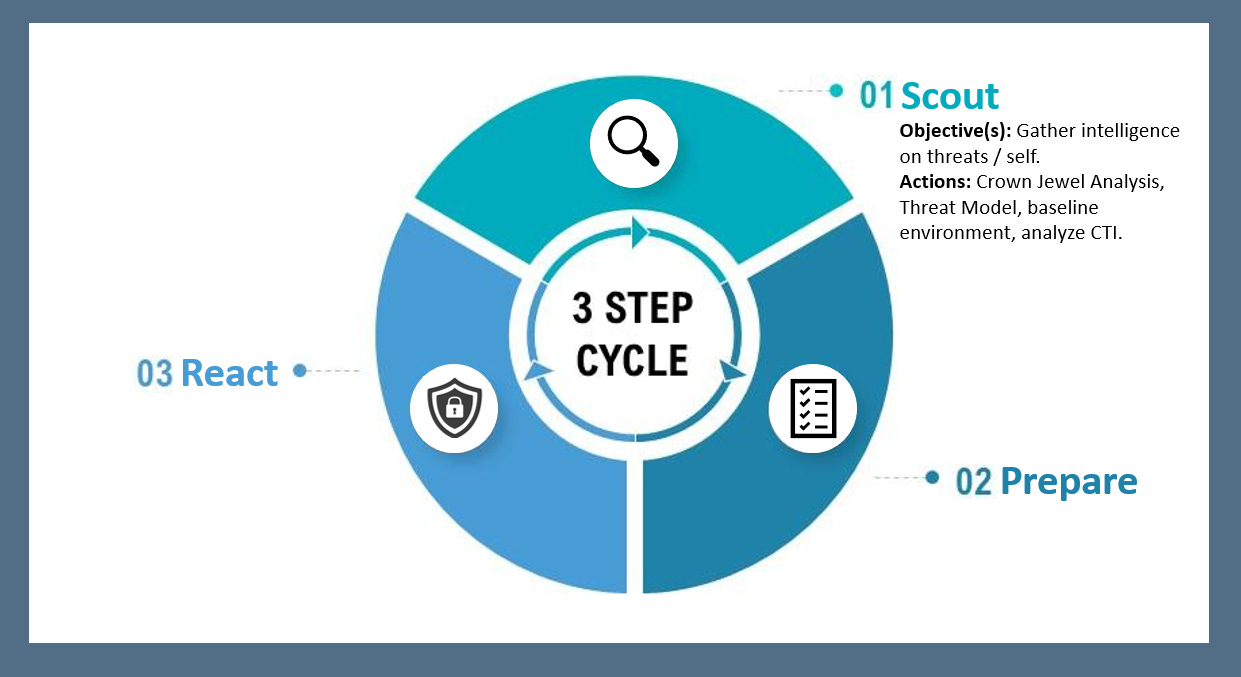
So how can this analogy be applied to cybersecurity to reduce the risk of threats? The answer to cybersecurity threats is not a new tool, a bigger team, AI, or even a bigger budget. There is no magic button to fix all the problems. There are many reasons for this, and the largest is that every environment and situation is unique, there is not a one-size-fits-all method for securing information, infrastructure, or systems. The best action that can be taken to attempt to mitigate the cyber threats of today and tomorrow is to incorporate a defensive security model of a scout, prepare, and react cycle that is run by practitioners who understand their unique situation and context, along with adversary mindset, goals, and techniques. That is the best defensive philosophy organizations can utilize to stand a decent chance of stopping breaches and threats.
How can a scout, prepare, and react cycle be used to stop intrusions and bolster defenses against their largest threats? This strategy incorporates threat-informed defense principles. Threat-Informed Defense (TID) is "the systematic application and deep understanding of adversary tradecraft and technology to prevent, detect, and/or respond to cyber attacks." TID emphasizes that an organization can improve and optimize cyber defenses by viewing those defenses from an adversary's perspective. A defense that does not scout the offense stands little to no chance of stopping them.
The rest of this blog will give a quick breakdown of each step, including practical use cases to complete them and questions to answer for each one.
Scout
In the Scout phase, the objective is to gather intelligence. We want to know our threats and confidently know our environment. This phase should include things such as a Crown Jewel Analysis to identify the critical data, processes, and systems of the organization. A baseline of controls, users, systems, and software must be completed, along with knowledge of normal user activity. To scout the adversaries, we will implement CTI collection and analysis procedures. Before we do that, the organization should conduct threat modeling to identify the largest threats to its mission and goals.
By completing this stage, an organization can know itself and know the enemy. Questions that should be answered in the Scout phase include:
Who are our top threats?
What are these adversaries doing?
How are they operating?
What are their goals?
What are our most important data types, systems, and processes?
How much money and time should be spent on securing them?
Who and What is in our environment?
What is normal activity in our environment?
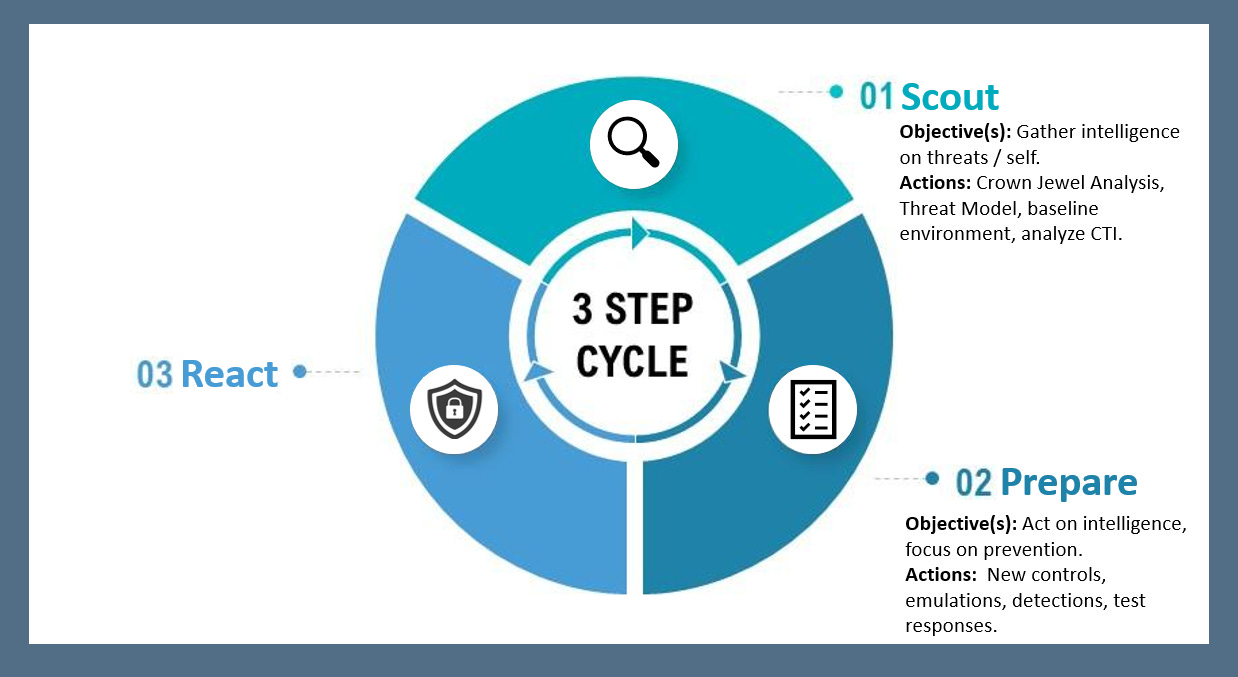
Prepare
In the Prepare stage, teams act on intelligence. This stage focuses on the prevention of future cyber-attack paths. An organization should review current controls and processes, run adversary emulations to test controls against actual TTPs, and then improve the areas that don’t prevent or detect adversary activity. Incident response measures should be tested and analyzed for improvement.
Questions that should be answered in the Prepare phase include:
Can we detect adversary activity in our network?
Do our preventative controls even work?
Can we run emulations?
Is our intel useful?
What is our ‘normal’ response time to incidents?
Do we have processes/time to patch based on intel?
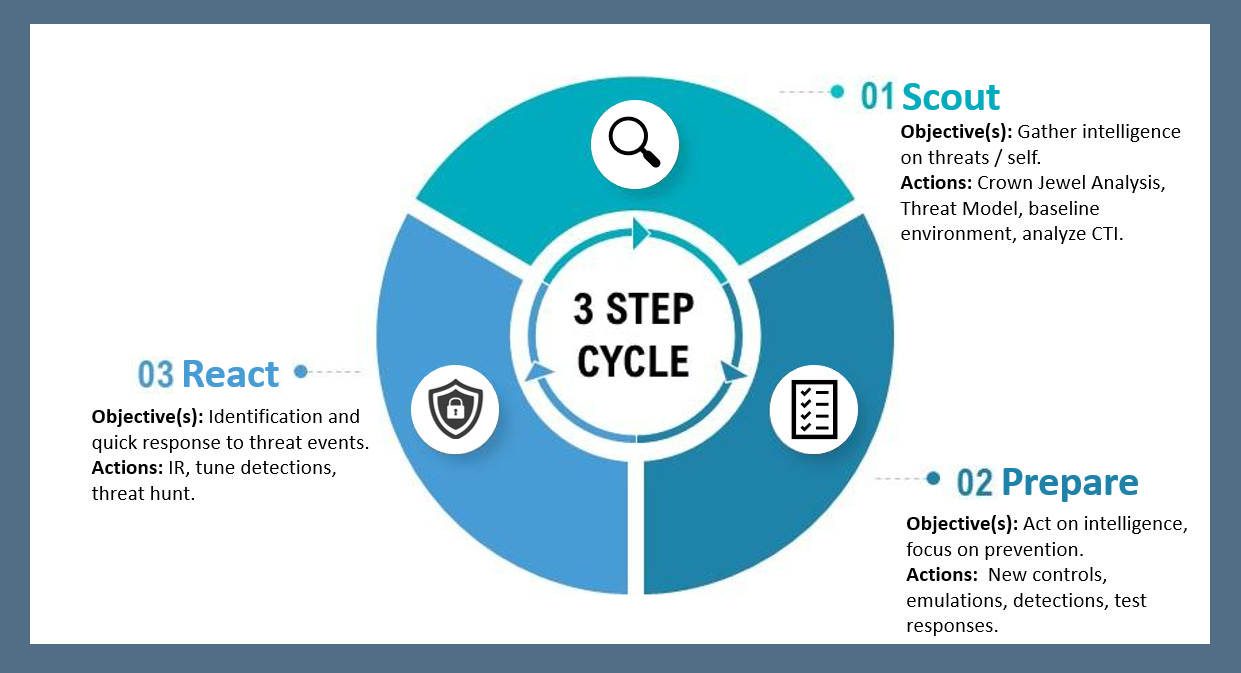
React
The React phase involves quick incident response capabilities and threat-hunting. The combination of a robust detection program and prompt incident response procedures will force adversaries to endure pain from the need to switch TTPs. This stage requires the ability to tune detections based on the environment, perform threat hunting to identify possible malicious behaviors that tools do not catch, and respond when an incident is identified or a hunt brings light to a compromise.
Questions that should be answered in the React phase include:
How noisy are our detections?
Can we react quickly to true positives?
Can we spot abnormal activity?
Do we collect the right data and look at what’s happening in the environment?
Do we know what to do and who to call when we see something?
Do we burden our adversaries by forcing them to move up the Pyramid of Pain?
What is Needed to Execute the SPR Cycle
Here is a short list of what is needed to properly utilize the Scout, Prepare, React cycle within an organization.
Management buy-in, good communication across the entire organization
Stakeholder time for a CJA
Security team time for threat modeling
Configuration and identity management
Control/environment baselines
CTI collection and analysis process
Red team/emulation capabilities
Purple team exercises that produce action items
Logs, SIEM, EDR for detections and threat hunting
Prepared incident response team, walk-throughs, practice
The complete mitigation of all cyber threats is not an achievable goal. An organization could patch everything every day, configure each system with top hardening practices, train each user to identify phishing and social engineering, and have the top EDR and network monitoring tools in place, and yet there will still be ways for intrusions to occur. A cyber defense team could never correctly anticipate, prepare, and react to every possible intrusion attempt or attack vector. Cyber defense is about improvement, not perfection. There is no destination in cybersecurity, but rather a journey of getting better each day.
Some days you hit a ball perfectly, and it is still caught at the wall. You can do everything “right” and still not win. That’s baseball, that’s life, and that’s cybersecurity.
Love it, disagree entirely, or think I missed something? Let me know